Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
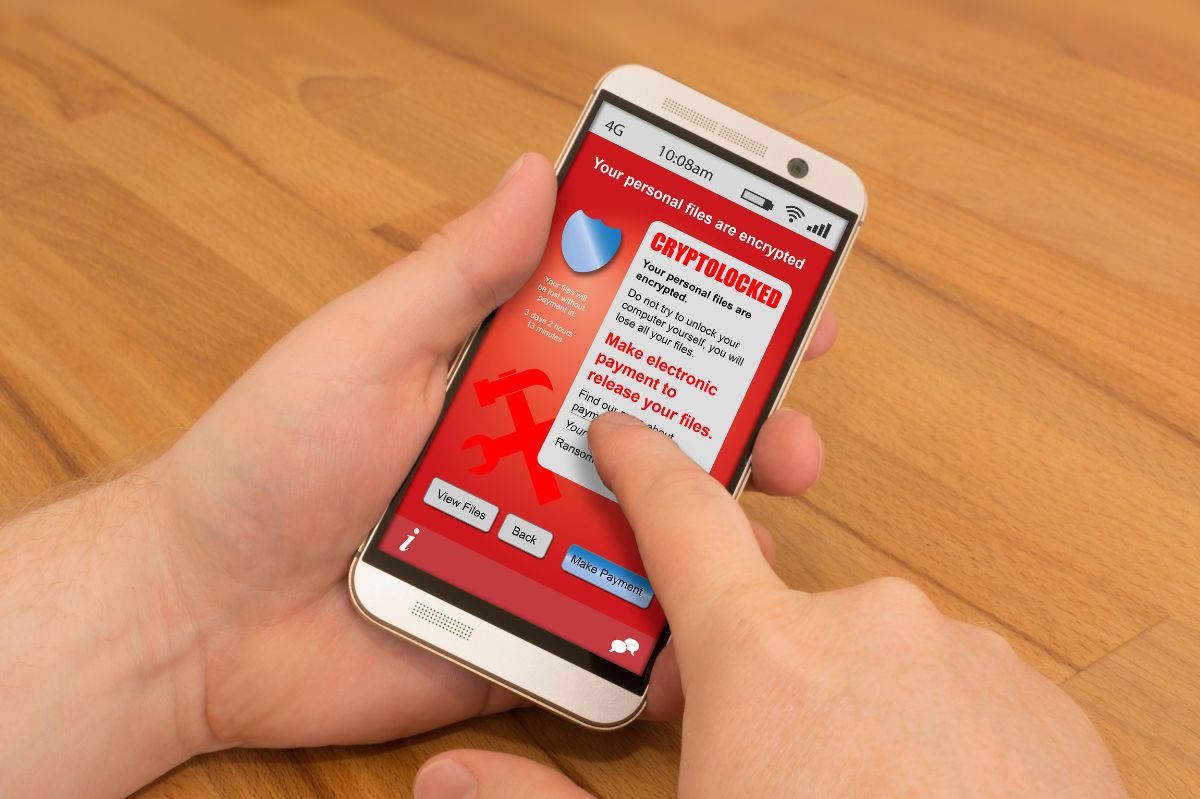
Finding a solution for a crypto-locker is becoming a priority for many companies when we consider the impact of malware and ransomware risks in terms of Business Continuity.
Several studies have found that in 2022 at least 58% of corporate PCs (globally) suffered cyber attacks from malware, i.e., dangerous software conveyed via the web. Specifically, over 50,000 company machines would have been infected by crypto lockers. After PCs and smartphones, ransomware is now also targeting servers. Morten Lehn, Managing Director of one of the most important players in the information security sector, recently declared that the future scenario would involve a new attack vector: infrastructure. That’s because most of a company’s valuable data is stored on data center servers. According to studies by Talos, Cisco’s threat intelligence company, about 3 million systems belonging to 1,600 networks, such as “schools, government agencies, airlines, and more,” would be at risk.
This type of ransomware does nothing but encrypt folders: in this way, users will find important encrypted files, from financial documents to family photos, up to entire company databases. To solve the locked computer problem, the user is asked to pay a ransom, hence the name of the ransomware.
This type of malware is distributed through numerous vectors, such as emails and exploit kits, which are malicious programs containing data or executable code capable of penetrating through one or more software vulnerabilities on computers, locally or remotely. Experts advise not to pay the requested sum also because cybercriminals often need to keep their word. In most cases, there are better solutions for a crypto locker.
Instead of giving in to payment demands, try to restore your files from backups made before encryption.
This results in a loss of all changes made since the last backup and could possibly lead to operational delays, hence the importance of frequent and monitored backups.
A good starting point can be what happened to the following Banco di Credito Cooperativo. Their main line of business was taken offline from a single workstation running Windows XP, now in the process of being decommissioned. Once the terminal was infected, the crypto locker began encrypting files on network shares. Fortunately, the server was a virtual machine that implemented a policy of full backups every hour. Having identified the moment of encryption, it was easy to identify the last available unencrypted backup. It was possible to restore a copy of the virtual machine in a few minutes, and the service was soon operational again.
In general, the best solution for the crypto locker is to prevent the risk of infection, relying on appropriate solutions capable of updating the protection as quickly as these threats transform and change. Therefore, using email security systems that scan and possibly block email attachments, together with an antivirus that guarantees real-time protection and detects suspicious activity in the background, preventive solutions could be implemented. With this in mind, it would be good practice to use restriction software that does not allow the launch of unwanted and, therefore, dangerous executable files, i.e., those not on our whitelist.
Furthermore, since malware usually exploits our systems’ vulnerabilities, it is advisable always to keep Patches updated to reduce the risk of infection.
Other good prudential rules, like the previous ones, are represented by monitoring outbound traffic by granting users the minimum privileges necessary to carry out their work and continuously updating the security settings of company software.
The most effective prevention measure of all, however, remains continuous company training to instruct employees on the correct identification of suspicious elements and the measures to be taken in the event of a risk.
Also Read : Neuro Linguistic Programming(NLP) In The Evolution Of Companies